Quantum Infinite is a Leader and a Pioneer in Post Quantum Cryptography Migration with Zero Data Friction and Air Gapped execution
Protecting financial assets against Quantum computing threats to encryption – Without moving a single byte of data. Fully aligned with NIST PQC compliance (FIPS 203, 204, 205) and U.S. federal cybersecurity mandates
"Quantum Infinite is a Trusted member of the Texas Bankers Association"

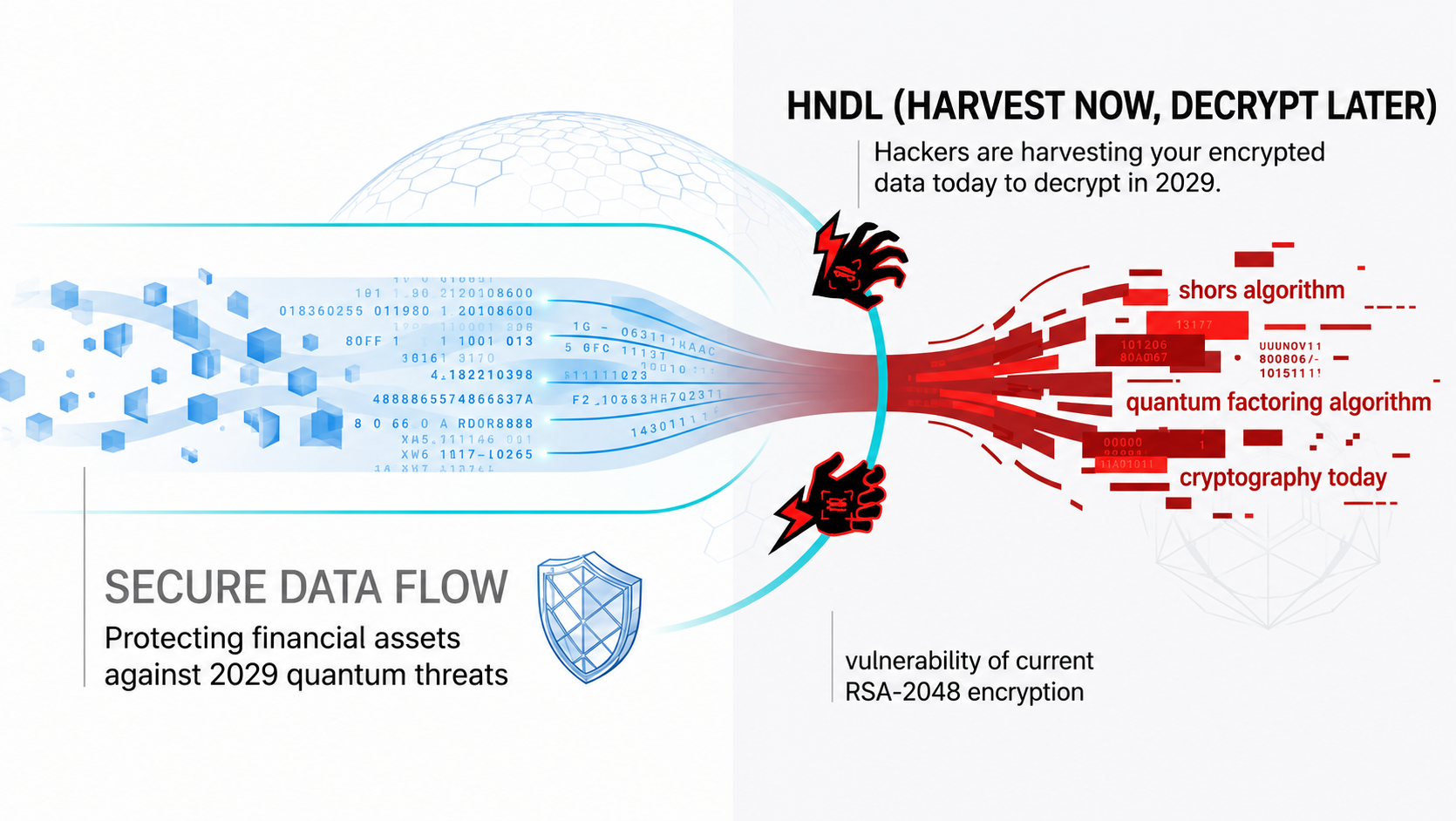
The HNDL Factor: Harvest Now, Decrypt Later
Your encrypted data isn’t safe – It is being collected right now for a Harvest Now, Decrypt Later attack. When Quantum arrives, your history becomes an open book.
The timeline has collapsed. What was once theoretical is now an active Quantum cybersecurity threat to financial institutions. Google’s 2029 mandate has compressed urgency, and RSA-2048 encryption is no longer security – It is delay. Quantum Resistant Cryptography is the future
The 2029 Timeline: Google’s accelerated roadmap means the “Q Day” is closer than ever
Adversaries are already executing Harvest Now, Decrypt Later attacks, rendering cryptography today as futile and capturing encrypted banking traffic today to decrypt it in 2029 when legacy encryption deprecates. This is not future risk – This is present exposure with delayed impact.
RSA and ECC aren’t protecting your data – They are buying time against Quantum computing threats to encryption you no longer have.
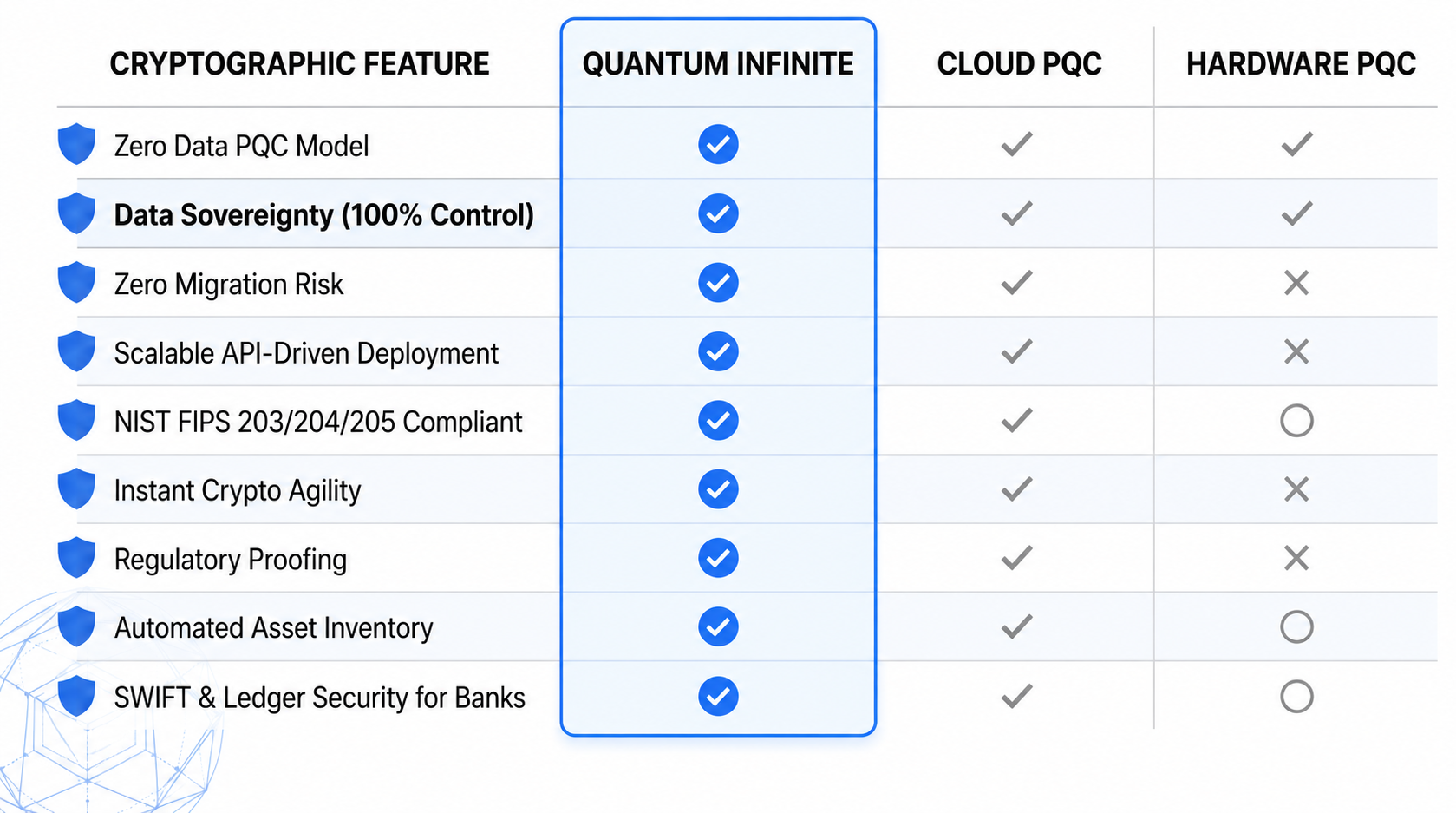
Built for the Architecture of Global Finance. Secured for the Quantum Era. We deliver Post Quantum Encryption by Air Gapped Zero Data PQC Encryption per NIST standards – Eliminating risk at its source.
Why the Zero-Data Air Gapped PQC Model Wins
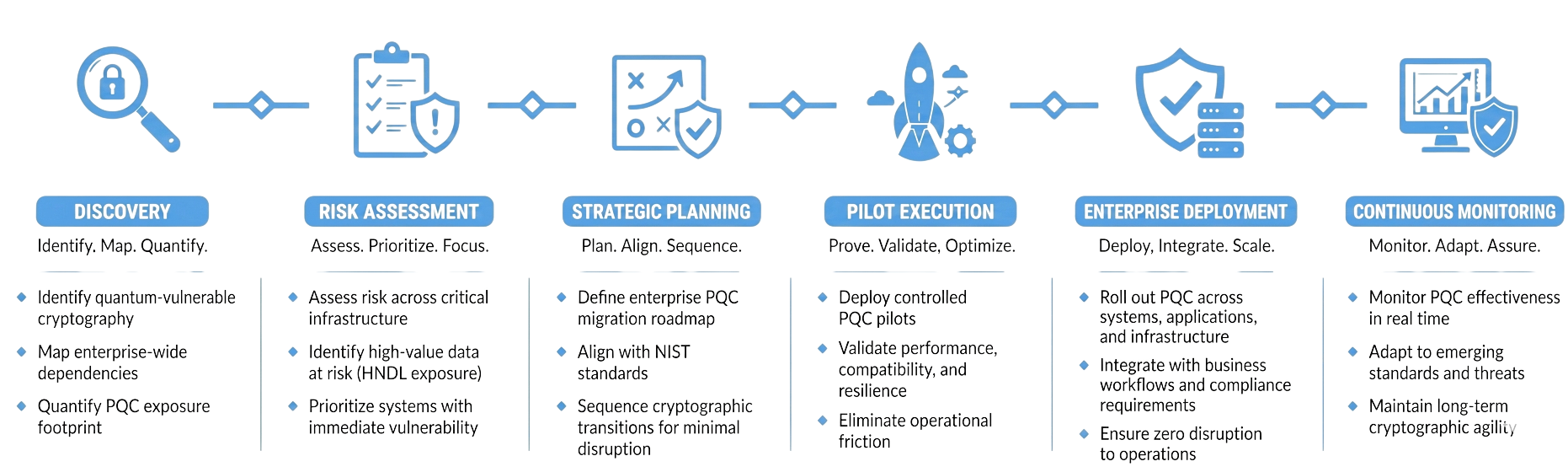
A Seamless Transition to Quantum-Safe
Quantum security is implemented as a layer – Not a rebuild. Our approach integrates seamlessly into your existing banking infrastructure with no disruption to operations, no downtime, and no impact to customers.
Built for the Architecture of Global Finance
Secured for the Quantum Era
We protect the world’s financial backbone with Air Gapped zero-data PQC, eliminating Quantum risk at its source – Without disruption, without data movement, and without delay.
WEB SERVER / URL ANALYSIS
EXPOSE. MAP. ELIMINATE RISK.
- Analyze all exposed web services, endpoints, and URLs
- Identify cryptographic usage and risk patterns
- Prioritize vulnerabilities with real-world impact
CODE BASE ANALYSIS
INSPECT. IDENTIFY. REMEDIATE.
- Deep inspection of application code and dependencies
- Detect weak or deprecated cryptographic libraries, algorithms, and implementations
- Eliminate hidden risks at the source
NETWORK ANALYSIS
ASSESS. ALIGN. ASSURE.
- Assess internal and external network communications
- Map cryptographic protocols in use across the network
- Identify gaps. Close them. Stay compliant
DIGITAL CERTIFICATE ANALYSIS
VALIDATE. VERIFY. PROTECT.
- Evaluate digital certificates, key lengths, algorithms, and trust chains
- Assess lifecycle status and expiration risk
- Ensure enterprise-wide certificate resilience
Standards for Private and Federal Agencies
Aligned with the latest U.S. Federal And Public Mandates for Crypto Agility



